No stress, our red team and vulnerability management platform have your attack surface covered
AI-powered continuous pentesting with built-in triage to cut
through noise and focus on what matters.
From vulnerability management to attack simulations and tailored services, everything is designed to strengthen your defenses against evolving threats. We adapt to your risk, maturity, and operational needs.
Built for teams that need to monitor, validate, and prioritize cyber risk—without building an in-house red team.
Protect your infrastructure by simulating real-world attacks at various scales—just like a hacker would.
Apply smarter, adaptive solutions to hardware vulnerabilities, and stay up to date with the latest discoveries in hardware hacking—especially in IoT devices.
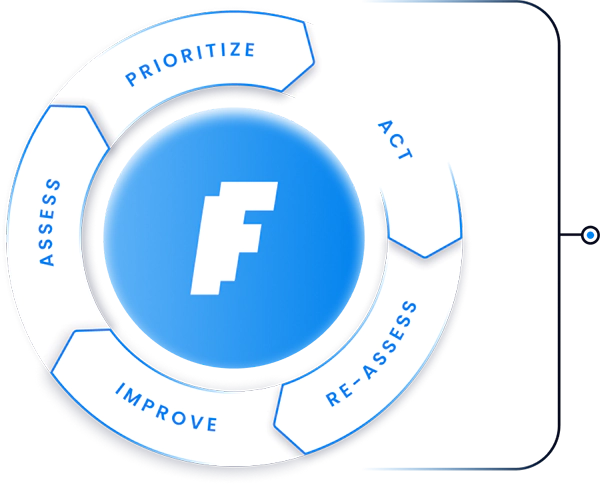
Faraday’s All-in-One offensive cybersecurity platform cuts operational overhead, accelerates remediation, and gives you full visibility across your attack surface.
Prioritize what matters. Context-driven vulnerability management powered by smart scoring.
Simulate real attacks. Continuous, automated testing to strengthen your defenses.
Map your digital exposure. External attack surface and threat intelligence in one place.
Think like an attacker. Tailored offensive security services, delivered by a team of seasoned experts.
We focus on cutting edge offensive cyber security techniques that go far beyond standard scanning to uncover vulnerabilities that others miss. We are not a conventional security firm.
Working since 2004 for that extra mile, we help organizations adopt an offensive mindset that ensures no rock is left unturned.
Your apps are the most common gateways for security weaknesses. We use a comprehensive suite of technical solutions to perform a professional assessment that guarantees a real map of vulnerable vectors.
Uncover hidden risks in your physical infrastructure with an offensive hardware security assessment conducted by experts.
Hardware and Software Security is not complete without closeness. An offensive art focused on detecting potential failures reviewing your on-site infrastructure.
The health of your networks compromises the health of your company. Our technical Red Team performs an exhaustive analysis detecting areas of critical risk.
Authentic Red Team in action. The art of deconstructing to rebuild the original equation. A reverse ride allows you to extract sources of real cyber threats for your most valuable applications.
Vulnerabilities are identified directly in your code, reviewing the software quality assurance. *We classify* them by risk, with advice on the best way to mitigate the general impact on your organization.
Your Applications can suffer a cyber-attack just like your Networks. We analyze your mobile architecture giving you a comprehensive map of vulnerable areas to remediate.
Validate your defenses against real-world attacks with penetration testing conducted by offensive security specialists.
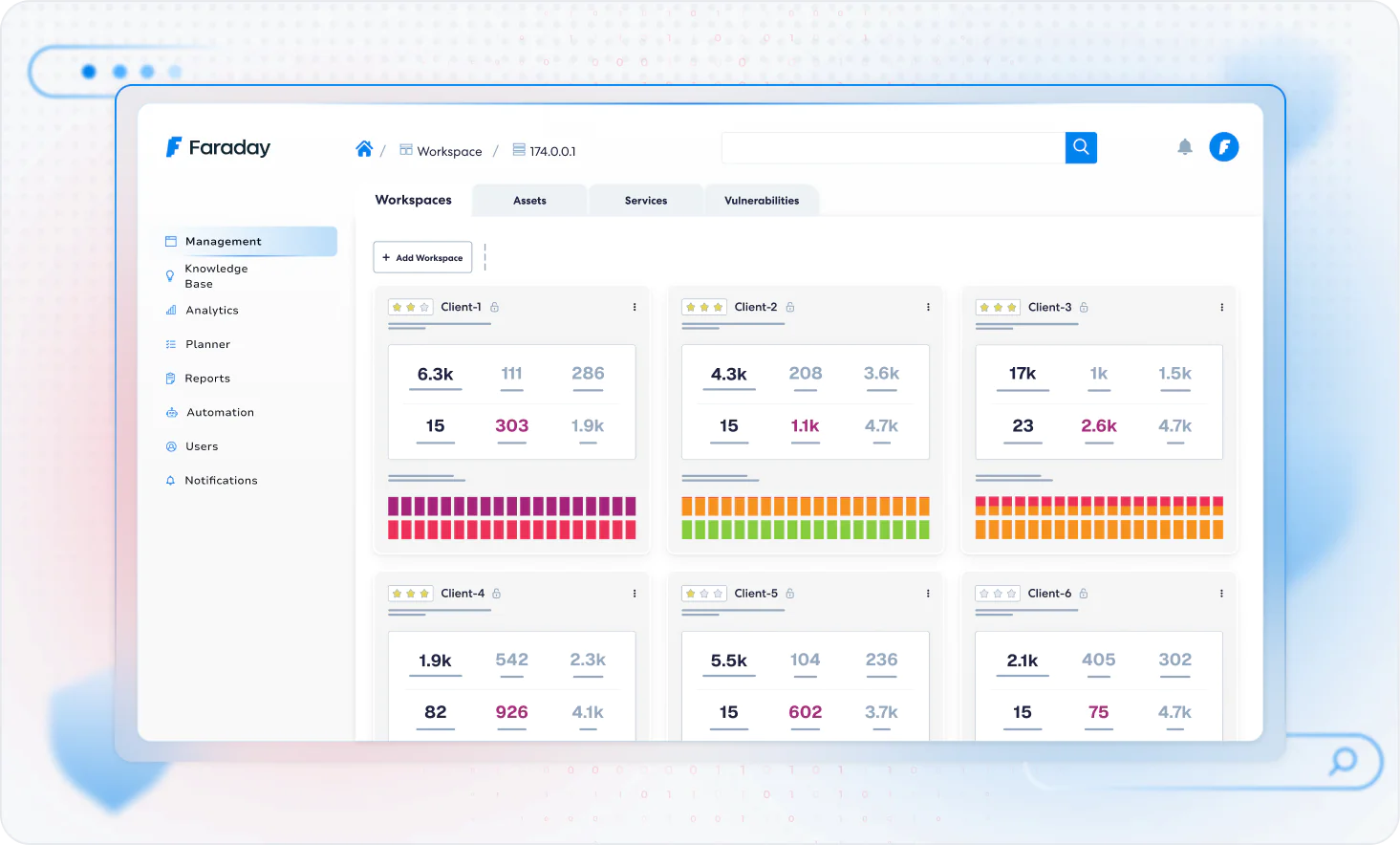
Faraday is your central hub for continuous security improvement. More than just scanning, it correlates findings with real risk, streamlines workflows, and connects security with operations. Fewer false alerts, more focus where it matters.
Showcase popular tools and platforms compatible with Faraday

Whether you’re exploring modular coverage or need expert validation, we’re ready to assist.
Tell us what you’re looking for — our team will respond shortly.